Control Center Security

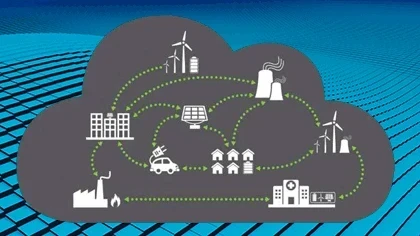
How utilities can protect bulk electric system control centers
BY ANDREW GINTER, Waterfall Security
While industry experts debate the likelihood of an attack against the power grid, the U.S. Department of Homeland Security (DHS) has already issued an alert that such threats are real and are on the rise. In fact, anything that is accessible directly or indirectly via the Internet is open to hacking, and the power grid is no exception.
Unfortunately, the information-technology (IT)-centric security practices of most utilities have not kept pace with the increasingly sophisticated network-based methods used by cyber attackers. Firewalls, anti-virus systems, security updates and other traditional safeguards are failing to defend against advanced persistent threats, widespread malware, and mundane attackers. Utilities need to find defenses that support business processes and operational processes without opening doors to allow attackers back inside reliability-critical control system networks.